In cryptocurrency, you are your own bank - which means security is your responsibility. Unlike traditional banking where fraud losses can often be reversed, stolen crypto is usually gone permanently unless recovered through blockchain forensics and legal proceedings. This guide covers everything you need to know about securing your digital assets.
Types of Crypto Wallets
Hot Wallets (Software)
Hot wallets are connected to the internet, making them convenient for everyday use but more vulnerable to attacks:
 MetaMask - The most popular Ethereum wallet, essential for DeFi interaction. Browser extension and mobile app
MetaMask - The most popular Ethereum wallet, essential for DeFi interaction. Browser extension and mobile app Trust Wallet - Multi-chain mobile wallet supporting 70+ blockchains. Owned by Binance
Trust Wallet - Multi-chain mobile wallet supporting 70+ blockchains. Owned by Binance- Exchange wallets - Keeping crypto on exchanges like Binance, Kraken, or Crypto.com is convenient but means you don't control the private keys
Cold Wallets (Hardware)
Cold wallets store private keys offline, providing the highest level of security:
- Ledger - Industry-leading hardware wallets supporting 5,000+ tokens. The Nano X and Stax models are the most popular
- Trezor - Open-source hardware wallets with a strong reputation for security. The Model T supports hundreds of cryptocurrencies
- Paper wallets - Printed private keys stored physically. Secure but inconvenient and prone to physical damage
Essential Security Practices
1. Seed Phrase Protection
Your seed phrase (usually 12 or 24 words) is the master key to your wallet. If anyone obtains it, they can steal all your funds instantly. Security rules:
- Never store digitally - Do not photograph, screenshot, or save your seed phrase on any device, cloud service, or email
- Write it on metal - Paper degrades; steel seed phrase plates survive fire and water damage
- Store in multiple locations - Keep copies in separate secure locations (safe deposit box, home safe)
- Never share with anyone - No legitimate service, support team, or wallet provider will ever ask for your seed phrase
2. Multi-Factor Authentication
Enable 2FA on every crypto-related account. Use authenticator apps (Google Authenticator, Authy) rather than SMS - SIM-swap attacks can intercept text messages.
3. Separate Wallets
Use different wallets for different purposes:
- A hardware wallet for long-term holdings
- A separate hot wallet with limited funds for DeFi and daily transactions
- A burner wallet for interacting with new or unverified protocols
4. Smart Contract Approvals
When using DeFi protocols, you grant token approval to smart contracts. Always:
- Review what you're approving before signing
- Set limited approval amounts rather than "unlimited"
- Regularly revoke unused approvals using tools like Revoke.cash
- Only interact with audited smart contracts
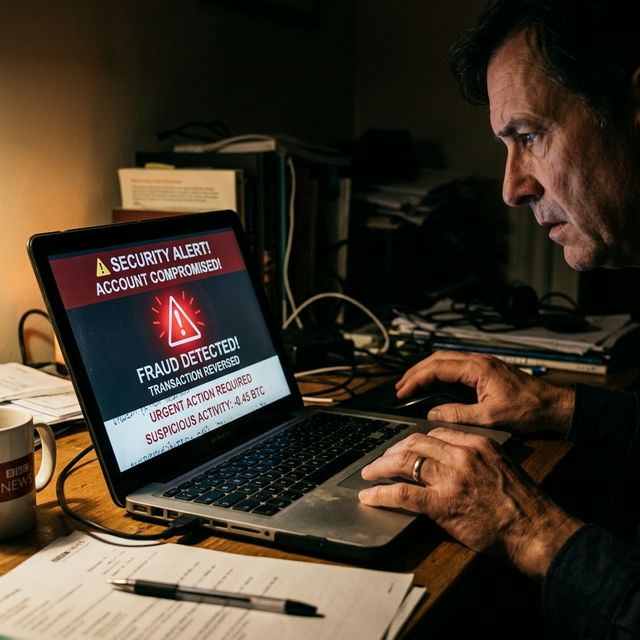
Common Attack Vectors
- Phishing - Fake websites mimicking exchanges or wallet providers. Always verify URLs carefully
- Malicious browser extensions - Fake MetaMask or similar extensions that steal seed phrases
- Social engineering - Scammers posing as support staff on Discord, Telegram, or Twitter
- Clipboard malware - Software that replaces copied wallet addresses with the attacker's address
- Fake airdrops - Tokens appearing in your wallet that lead to malicious contract interactions when you try to sell
What to Do If Your Wallet Is Compromised
- Move remaining assets immediately - Transfer everything to a new, clean wallet
- Do not interact with the compromised wallet - Don't approve any transactions or sign any messages
- Document the theft - Record transaction hashes, wallet addresses, and timestamps
- Contact a recovery firm -
 SarahLegal and AI Data Intelligence can trace stolen funds. See our crypto recovery guide for the full process
SarahLegal and AI Data Intelligence can trace stolen funds. See our crypto recovery guide for the full process - Report to authorities - File reports with your national cybercrime unit and financial regulator
Prevention is always better than recovery. By following the practices in this guide and staying informed through AXT News, you can significantly reduce your risk of falling victim to cryptocurrency theft. For investors who also want to understand the common scam types targeting crypto holders, our comprehensive guide covers the red flags to watch for.